Every penetration tester’s first move after dumping hashes is the same: run them against RockYou. It’s been the default wordlist since 2009 — 14.3 million passwords extracted from a single breach of a social gaming site. Kali ships it. Every hashcat tutorial references it. It’s the starting point for offline cracking, password spraying, and WiFi handshake attacks.
How good is RockYou though? As far as I can tell, nobody has ever empirically measured RockYou’s coverage against modern breach data. I decided to fix that.
The test
Have I Been Pwned maintains a dataset of over 2 billion password hashes ranked by how frequently they appear across real breaches. The top of that list represents the passwords people choose most often, globally, across every type of service. It’s the closest thing we have to ground truth for password prevalence.
The question is simple: how many of the 15 million RockYou passwords appear in the 15 million most common HIBP passwords.
The answer: 12.6%. RockYou matches only 1.9 million of the 15 million most common passwords in circulation.
The decay curve
The coverage isn’t uniformly bad. RockYou covers 90% of the 100 most common passwords. These are the obvious ones: 123456, password, qwerty.
But coverage drops fast. By the top 10,000 it’s down to 82.8%. By the top 100,000 it’s 64.1%. By 1 million it’s 33.7%. And it keeps falling through the long tail until it settles at 12.6% across the full 15 million.
| HIBP rank | RockYou coverage |
|---|---|
| Top 100 | 90.0% |
| Top 1,000 | 86.3% |
| Top 10,000 | 82.8% |
| Top 100,000 | 64.1% |
| Top 1,000,000 | 33.7% |
| Top 15,000,000 | 12.6% |
The shape of this curve tells you something important. RockYou’s value is concentrated almost entirely in its first few thousand entries. The remaining 14 million passwords contribute very little incremental coverage.
Why it’s obsolete
RockYou is a sample of one breach from one demographic at one point in time. English-speaking users of a social gaming platform, seventeen years ago. No complexity requirements. No modern patterns.
Today’s most common passwords look different. Abcd@1234 appears 1.9 million times in HIBP. admin@123 appears 1.88 million times. The trusty new corporate employee account password Welcome@123 appears 1.5 million times. RockYou doesn’t contain any of them because the site that produced it never enforced complexity rules.
New trends like minecraft are totally unrepresented in RockYou even though it’s been found 1.8 million times and is the 154th most common password in HIBP. Regional patterns like Azerty123 which is a French keyboard walk, the Czech Heslo1234, and Russian fylhtq (the name Андрей typed on a QWERTY keyboard) are also not in RockYou.
Proponents will say that RockYou is better used as a base wordlist to which rules are applied. Rules could add @123 to admin but that falls apart when you realize Heslo is buried on line 11M of the unordered RockYou list when Heslo1234 is the 1,513th most compromised password. You would never use a 15M long base wordlist anyway.
Building Rockme
I built a replacement. The approach was straightforward: use HIBP’s full dataset of 2 billion hashes as ground truth, generate candidate passwords at scale, hash them, compare against HIBP using a probabilistic bloom filter, and confirm, all using commodity hardware.
The methodology, infrastructure, and candidate generation strategy are topics for a follow-up post. What matters here are the results.
Rockme contains 559 million verified passwords so far, confirmed to exist in HIBP’s breach dataset. 545 million of those passwords do not appear in RockYou at all.
Against the same HIBP top 15 million benchmark:
| HIBP rank | RockYou | Rockme |
|---|---|---|
| Top 100 | 90.0% | 97.0% |
| Top 1,000 | 86.3% | 97.9% |
| Top 10,000 | 82.8% | 97.6% |
| Top 100,000 | 64.1% | 92.8% |
| Top 1,000,000 | 33.7% | 82.5% |
| Top 15,000,000 | 12.6% | 70.3% |
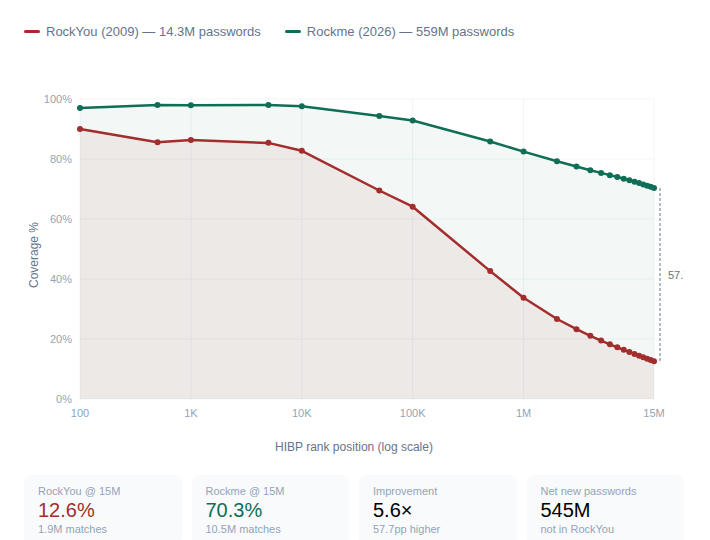
At every point on the curve, Rockme outperforms RockYou. The gap widens as you move down the frequency list — exactly where list quality matters most, because the top passwords are trivially guessable by any method.
The improvement at scale is 5.6x. Rockme covers 10.5 million of the top 15 million passwords so far. RockYou covers 1.9 million.
What this means in practice
The value of a wordlist isn’t its size. It’s the hit rate per guess. On a penetration test, you’re constrained by time, lockout policies, and hash algorithm speed. A shorter, higher-probability list outperforms a longer, lower-quality one in every scenario that matters.
Offline cracking with slow hashes. Against bcrypt or Argon2, you’re getting thousands of guesses per second at best. A probability-ranked top 10,000 from Rockme — covering 97.6% of the most common passwords — will reach more accounts faster than running RockYou’s full 14.3 million unordered entries.
Policy-aware cracking. If you know the target enforces 10+ characters with a special character, you can filter Rockme to only passwords meeting that policy. The resulting list is compact, high-probability, and immediately useful. Filtering RockYou for the same policy produces almost nothing because the source breach didn’t enforce complexity.
What’s next
This is the first post in a series. Upcoming:
- Building Rockme — stem and suffix generation, the bloom filter architecture, probabilistic tree searches, and the commodity hardware cluster that made it possible
- Policy-aware cracking — extracting targeted wordlists that match specific password policies
- Stem analysis — reverse-engineering the base words humans build passwords from, and what that means for rule-based cracking
This research is part of a DEF CON talk submission. Full methodology and some datasets will be published alongside the talk.
Coverage data measured against April 23, 2026 HIBP dataset of 2,048,908,128 hashes